Best Practices to Help You Stay Cyber Safe: How to Stay Safe Online

Cybersecurity Awareness Month was created to raise awareness about the importance of cybersecurity and to educate internet users on how to stay cyber-safe. Following best practices for cyber security is critical since we spend an average of 145 minutes per day online. In this blog post, we review recommended best practices that will help enhance your cybersecurity profile and teach you how to stay safe online.
Be Cyber Smart! Practice these top tips to stay safe online and help keep yourself cyber-safe.
Use appropriate passwords:
Using unique passwords for each of the various sites you access is an important safe online habit. Studies show that 59% of internet users incorporate their name or birthday into their passwords making it 27% more likely to be guessed by a hacker. This significantly increases the chances of personal information being stolen. Using the same password for multiple sites may allow a hacker to breach more than one of your accounts. Creating and choosing passwords that adhere to the following guidelines is another critical component of appropriate password discipline:
- Use a different password for each system and platform you access.
- Use longer passwords. It has been proven that password length is a crucial element of creating hard-to-crack passwords.
- Make your passwords complex; use a mix of uppercase and lowercase letters, numbers, and symbols.
- Reset your passwords every few months.
- If you use a password management application, be sure to choose a reputable provider and be certain to keep your credentials to the app secure and backed up.
Employ anti-virus or anti-malware software:
Installing anti-malware or anti-virus software on your computer can help reduce the chances of your computer being compromised by identifying and preventing the installation of malware and ransomware. If you use this kind of protection, it is extremely important to keep the software updated and current with the latest version. Setting up automatic updates and upgrades is a good way to keep your protective platforms working to keep intruders out.
Enable multi-factor authentication when available:
Multi-factor authentication (MFA) or two factor authentications (2FA) requires a user to provide at least two pieces of evidence to prove their identity. This stepped-up authentication provides another layer above simply using a username and password to access an online resource. Providing a phone number or email as a second means of confirming your identity reduces the probability of your account being compromised. Many MFA implementations also have time limits and expirations which makes it even more difficult for a bad actor to access your account. 57% of companies use MFA to keep their customers and employees safe. Enabling MFA or 2FA adds an extra layer of security to help you stay safe online.
Stay up to date:
Keeping your computer and mobile devices updated is important for a few reasons. It can help identify security issues, remove any malware that may be affecting your devices and keep your information safe. Software updates can be released at any time and tend to be more frequently released on IOS and Android mobile devices. Many of these updates include patches to already installed software and apps. Most devices can automatically install small updates but sometimes need information and credentials from you to apply the update. Remember to check for updates regularly on your devices to keep you cyber safe!
Phishing Attacks

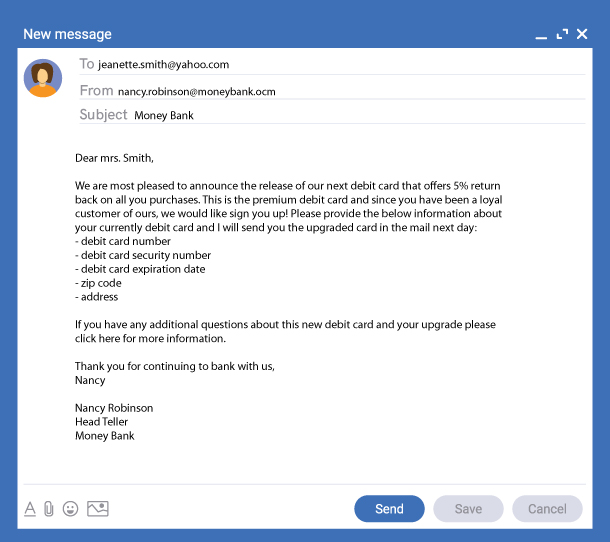
Phishing attacks use strategically crafted emails or malicious websites in an attempt to collect personal information or infect your device with malware or ransomware. In 2020, phishing was the most common attack carried out by cyber-criminals. The Internet Crime Complaint Center found that phishing was the most frequently used attack in 2020 with more than 240,00 victims. Always be on the lookout for indications that an email or a website might be a phish:
- Suspicious sender’s address – Cybercriminals will often use email addresses or create website URLs that closely resemble a legitimate company’s email or website domain. Look for spelling errors in the address or incomplete words. Some examples could be misspelling “.com” as “.ocm”. Misspelling the name of the company is another common sign of an impersonated email or URL.
- Phishing hyperlinks – If you come across an email with a hyperlink, hover over the link first to make sure the link matches the text, if it does not, or is linked back to a website that you don’t recognize or doesn’t make sense, do not click or follow the link.
- Spelling, grammar, and layout – Spelling and grammatical errors and layout issues can be a sign of phishing attempts. Reliable companies will not have these errors as they go through many steps of review and proofreading to ensure the messaging is right.
- Attachments – Attachments and requests to download files are common mechanisms employed for distributing malware. These emails often convey a sense of urgency to encourage you to download and open the attachment. Be cautious and look for indicators that the request may be malicious.
Spoofing 101
Spoofing is when someone impersonates a reliable source to try to build trust and gain information. Whether it is a text message, email, or phone call, spoofing can be easily overlooked as authentic communication. Watch out for misspelled words, unusual phrases, and inconsistent langue to help spot these spoofers. If the company looks familiar but the sender does not, call the company to verify the contact. This is just one example that can help prevent you from accidentally sharing information.
Practicing safe cybersecurity is important. In 2020 alone, more than 300 million people were impacted by some type of cybersecurity breach. According to Define Financial, nearly 1.4 million identities were stolen in 2020. Make sure to be cautious when opening emails, examining suspicious links, and sharing your personal information over the internet.
Mid Penn Bank is Dedicated to Helping Your Stay Cyber Safe
Mid Penn Bank is committed to keeping your money and your information safe. With enhanced security features and real-time alerts, our platforms and apps give you peace of mind and provide tools to monitor activity and keep you informed. If you think you have fallen victim to any type of compromise of your accounts, or if you have questions about online banking safety, contact us through our call center at 1-866-642-7736.
https://www.pingidentity.com/en/company/blog/posts/2017/what-is-multi-factor-authentication-mfa.html
https://security.berkeley.edu/resources/best-practices-how-to-articles/top-10-secure-computing-tips
https://www.forcepoint.com/cyber-edu/spoofing
https://www.definefinancial.com/blog/identity-theft-credit-card-fraud-statistics/
Share:
Disclosures
The material on this site was created for educational purposes. It is not intended to be and should not be treated as legal, tax, investment, accounting, or other professional advice.
Securities and Insurance Products:
NOT A DEPOSIT | NOT FDIC INSURED | NOT BANK GUARANTEED | NOT INSURED BY ANY FEDERAL GOVERNMENT AGENCY | MAY LOSE VALUE
